Ransomware protection: What companies should do
Your computer and other electronic devices can be put under various digital threats. One of them is a type of malware called ransomware.
Different factors may make you a potential victim of this.
It could be that your device is not state-of-the-art anymore, or its software is outdated. Another possibility is your cybersecurity may not be receiving sufficient attention.
However, there is no need to worry about this particular type of malware as long as you deploy ransomware protection.
Ransomware protection prevents cybercriminals from executing successful ransomware attacks on your devices. It involves tools, techniques, and technologies that help protect your networks.
An adequate version starts with implementing basic security etiquette, such as network cybersecurity measures, strong authentication, and malware protection.
Further, companies can build on this secure foundation by adding protocols devoted to avoiding ransomware attacks and recovering from them.
This article sheds light on ransomware, its types, and the steps individuals and companies can take to ensure ransomware protection for their devices.
What is ransomware?
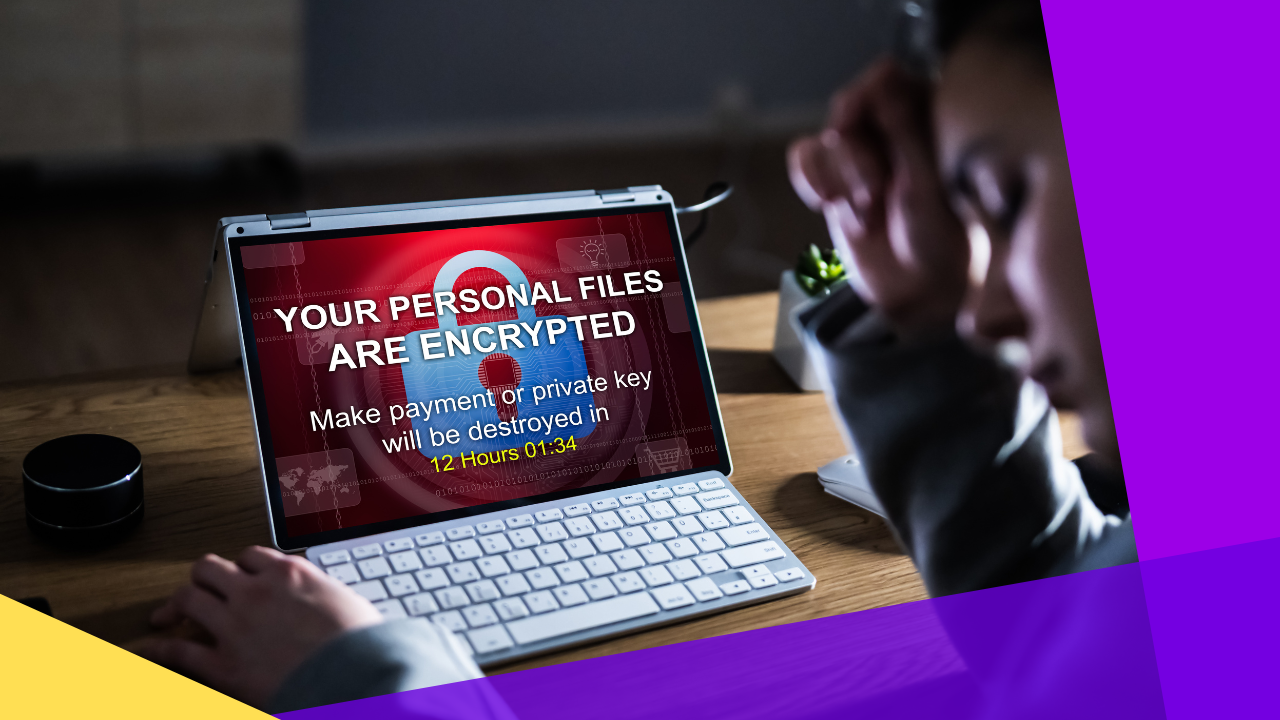
Ransomware is a malware threat that encrypts one’s files or locks the operating system. Infection can happen in many ways, including:
- Unsafe and rogue websites
- Software downloads
- Spam mail
Once ransomware gets ahold of a digital hostage, it demands payment for its release. The victim won’t have access to them until they pay the requested amount, hence its unabbreviated name, “ransom malware.”

After the initial infection, ransomware may also spread to connected systems, such as other accessible computers and shared storage devices.
If the demands aren’t met, the encrypted data will usually remain unavailable to the victim. In some instances, even after a ransom is paid, threat actors will demand additional payments, delete a victim’s files, or refuse to give access back.
History and evolution of ransomware
The earliest forms of ransomware were developed in the 1980s. Ransom payment was sent by post. The victims were individuals with their personal devices.
Eventually, however, cybercriminals began to realize the full potential of ransomware when they used it on companies.
This operation slowed down organizations’ productivity and resulted in data loss. In turn, the attackers gained revenue. It turned out to be a great success for them, so much so that cybercriminals started diverting most of their attacks toward companies.
At present, ransom payments are demanded to be sent through cryptocurrency or credit cards. Some cybercriminals even make a business out of ransomware, selling it as a service known as Ransomware-as-a-Service or RaaS.
3 types of ransomware
Knowing more about what you’re dealing with is the best first step in fighting against it.
Outlined below are the three common types of ransomware:
Encryptors or crypto-ransomware
Encryptors are one of the most damaging and well-known types of ransomware.
They encrypt files and data within a system, rendering them inaccessible without a decryption key. Then, payment will be demanded in exchange for getting entry back.
Once cybercriminals get ahold of your data, no security software or system restoration app can return them to you. This is why encryptors are dangerous.
Unless you pay for the ransom, your files are gone. As mentioned earlier, paying up doesn’t guarantee you get your files back, either.
Screen lockers
Lockers completely freeze you out of your computer’s system. They remove your access to files and applications.
Screen lockers come in the form of a lock screen displaying a ransom demand, sometimes with a countdown clock. This increases urgency and drives victims to take action.
Scareware
Scareware includes fraudulent security software and technical support scams.
It is a fake program that claims to have detected a virus or some other issue on your computer. Then, it directs you to pay to resolve the problem.
Some types of scareware lock the computer, while others overload the screen with pop-up alerts.
However, your files won’t actually get damaged. Scareware only aims to make you paranoid enough to pay money.
When confronted with potential scareware, think logically: A legitimate cybersecurity software program wouldn’t solicit customers the way a scareware software does.
Additionally, if you haven’t installed the software that scareware is imitating, then you should know that the pop-up alerts are fraudulent.
Now that you know more about the enemy, you’re ready to take the appropriate steps to fight it. The following sections explain how to implement ransomware protection.

How to prevent ransomware infection
“Prevention is better than cure” also applies to your devices’ cybersecurity.
Practice proactive ransomware protection by doing the following:
Keep your software and OS up-to-date
Regularly updating software and operating systems helps to protect you from any malware.
When downloading updates, make sure to also benefit from the latest security patches. This makes it more difficult for cybercriminals to exploit vulnerabilities in your programs.
Use preventative software programs
Install antivirus software on your devices, along with firewalls and email filters. This reduces malicious network traffic. Remember to keep these programs updated for optimized use.
Keep personal information safe
Don’t reply to untrusted sources (texts, calls, emails) requesting personal information. If you do, cybercriminals may try to use the information to tailor phishing messages directed to you.
Do not open insecure links and suspicious email attachments
Clicking links in spam messages or on unknown websites is unsafe. If you happen to click on a malicious link, an automatic download for ransomware could be started.
Additionally, avoid opening any fishy-looking email attachments. This may result in a malicious macro that gives malware control of your device. And then, curiosity will have killed the cat.
Refrain from using unknown USB flash drives
Never connect unfamiliar flash drives or other storage devices to your computer since they may already be infected. Practicing this avoids the risk of any type of malware or virus.
Only download from known sources
Don’t download files from insecure sites. This minimizes the risk of downloading ransomware. Depend on verified and trustworthy sites for downloads.
You can tell a website is safe by an accompanying badge that indicates so, usually in the form of a shield or a lock. Also, make sure the website uses “https” instead of “http”.
Educate yourself
Keep yourself informed about the latest updates regarding ransomware.
There may be new strategies being developed by cybercriminals to spread this type of malware. If there are, it’s better to be prepared.
Maintaining awareness of the topic will make it easier to adapt and implement new ransomware protection strategies of your own.
What companies should do for ransomware protection
Ransomware infections can pose a threat to businesses of all sizes.
Organizations that fall victim to ransomware usually have poor security systems. This makes attacking them easier and more tempting to cybercriminals.
Here are some actions that should be considered in establishing ransomware protection:
Train your employees
Educating employees on ransomware protection will help your company to avoid getting attacked. A worker who’s equipped with sufficient knowledge about ransomware will be more effective at countering related attacks.
Another action to take is implementing a security protocol that enables your employees to assess whether an attachment or link is trustworthy.
Stay up-to-date
As mentioned earlier, keeping a device’s software and operating systems can help avoid ransomware attacks. Make sure this is applied in your whole company, done by each department regularly.
Make use of cloud technology
Vulnerabilities in cloud-based systems are harder to exploit, putting them at an advantage over on-premise systems.
Cloud storage technologies also allow you to restore earlier versions of your data. This implies that if those files are encrypted by ransomware, you should be able to return to their unencrypted versions via cloud storage.
External storage back-up
Whether to prevent malware or just in general, it’s always important to back up business-critical files to external devices, such as hard drives and flash drives.
Similar to cloud storage, external devices don’t depend on a specific computer for access.
In the case that your organization has already been infected with ransomware, report the incident to your IT department immediately.
Secure your company’s data and networks with ransomware protection
Knowledge is power. Confidential files, personal information, and every other type of valuable data inside each of your organization’s computers all ultimately contribute toward your success.
Because of this and other significant reasons, the security of your company should place high on your priorities. Don’t wait around to experience ransomware first-hand.
Follow the precautions discussed in this article. Take preventative actions by implementing ransomware protection strategies.
While you’re at it, educate yourself and your employees regarding other types of malware. Develop corresponding protocols to prevent them from encrypting your files.
By doing these, you will be securing your business’ data along with your clients’.




 Independent
Independent




