Protect your business with data network security solutions
The importance of data network security cannot be overstated.
Everyone consumes, transfers, and stores information at home or the office. Social media, work emails, and online banking are some of the most common activities that, without most people noticing, are constantly threatened by data breaches.
As a business owner, the stakes are made higher in protecting your network. Your brand reputation and revenue opportunities could be derailed in the event of a cybersecurity problem.
This article aims to walk you through the value of data network security and why you should keep an eye on the latest technologies and best practices.
Data and network security in a nutshell
While usually bundled together, data security and network security are two distinct fields.
Data security protects digital information, often stored in a device or a database, from unauthorized access and other problems that could compromise them.
On the other hand, network security covers your IT infrastructure, including those responsible for your network traffic and data transmission.
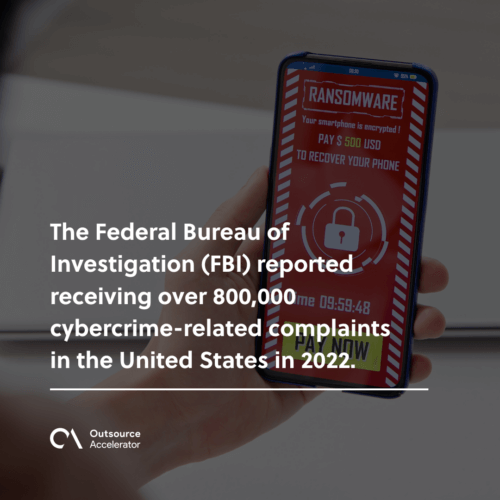
The Federal Bureau of Investigation (FBI) reported receiving over 800,000 cybercrime-related complaints in the United States in 2022. This translates to losses exceeding $10 billion.
Since most businesses require online access to function properly, controlling who gains access to your network and data storage facilities is crucial.
Together, data network security measures protect your company in the digital space. Below are some of the components of your cybersecurity program:
- Endpoint detection and response (EDR) – In a world where businesses support remote and hybrid working arrangements, remote devices are considered endpoints that require specialized security and monitoring measures.
- Cloud and on-premise security – Cloud computing refers to IT services accessed and delivered through the cloud. In contrast, on-premise and more traditional setups require hardware and equipment stored on your business premises.
- Compliance – Depending on which country you operate, there are regulations concerning the handling, transmitting, and storing of information. For example, HIPAA was primarily enacted to protect sensitive patient information.
- Data backup and disaster recovery – Whether it’s a cybersecurity attack or an act of nature, keeping backups and rapid restoration capabilities help organizations recover more quickly.
- Social engineering – Keeping your employees well-informed, trained, and oriented minimizes the risks of them exposing your network to malicious entities.
Benefits of updated security practices
Keeping your IT infrastructure secure is a continuous process, like a cat-and-mouse chase between hackers and security professionals.
Imagine an average of 560,000 new harmful programs (malware) being detected daily. This translates to over 5.5 billion attacks around the world.
With threats to data network security everywhere, here are a few advantages of updating your security systems.
Protect sensitive information
Protecting sensitive information can spell the survival or ruin of a company operating in regulated industries. Finance, energy, transportation, manufacturing, and healthcare are some spaces expected to take their data network protection very seriously.
This does not mean that other businesses can take it easy. Employment and health records for your employees, financial transactions, and trade secrets are crucial data businesses everywhere have to deal with.
It could have serious consequences if you somehow lose access to this information or have them leaked on the Internet.
Compliance with existing laws and standards
As mentioned, compliance is a key component of full security solutions. Industry standards and government regulations outline what full-fledged businesses should be capable of.
Similarly, industry certifications consider data network security capabilities as a part of your organization’s quality management practices.
Aside from your company’s compliance with the government and the industry, data governance and compliance also extend to your company.
Outlining the proper use and access of information for employees helps minimize risks and improve process efficiency.

Minimize risks of process disruptions
One common form of malware is ransomware, which holds your system hostage unless you pay the attackers.
A 2023 cybersecurity report reveals that companies usually experience downtimes of seven to 21 days following a ransomware attack. These downtimes translate to lost productivity and, ultimately, lost revenue.
By setting up data network security practices, you set up your systems and organization to prepare and adapt to these untoward incidents.
Preserve brand reputation
Most businesses operate digitally: e-commerce websites, mobile apps, and social media pages. Whatever they release on these platforms affects how the market sees them, the consumer’s purchasing decisions, and their revenue.
The potential business impact of these online activities is referred to as the social currency. A bad security breach could wipe everything out and put customers at risk.
Customers and stakeholders might find your business unreliable without robust data network security measures. This impact is harder to measure quantitatively but has been identified as the fourth most common threat to reputation.
Prevent damages and lawsuits
Aside from negatively affecting your reputation, failure to protect your data and network could lead to legal action. If it can be proven that you have neglected your duties, whether to your customers or your employees, a lawsuit can be filed against you.
Imagine the damages that a single data breach could cause. Leaked personal, mailing, and banking information could be used for identity theft, affecting over 15 million Americans in 2021.
Setting up data network security for your business
Data network security should never be taken lightly, regardless of your enterprise’s size and industry.
Aside from protecting your business interests, these measures protect your employees and customers. By adhering to existing regulations and standards, you can ensure efficient operations with minimal risks of being at risk.




 Independent
Independent




